Big enough to deliver, with a dedicated team small enough to care
We operate across the jurisdictions you need. Our global reach means your requirements can be taken care of 24/7
View all locationsAsset classes & fund types
Impact funds Digital assets Energy and infrastructure Hedge Hybrid funds Real Assets Services Private debt and credit Open-ended funds Private equity and venture capital View full offeringKey services
Alternative investment fund manager (AIFM) services Anti-money laundering services Asset servicing Closed-ended fund administration services Data services ESG services Know your customer services Portfolio monitoring and reporting Technology services Depositary services Regulatory compliance servicesAsset Owners
UHNW
Foundation and endowments
Pension Funds
Sovereign Wealth Funds
Supranationals
View full offeringFund & Asset managers
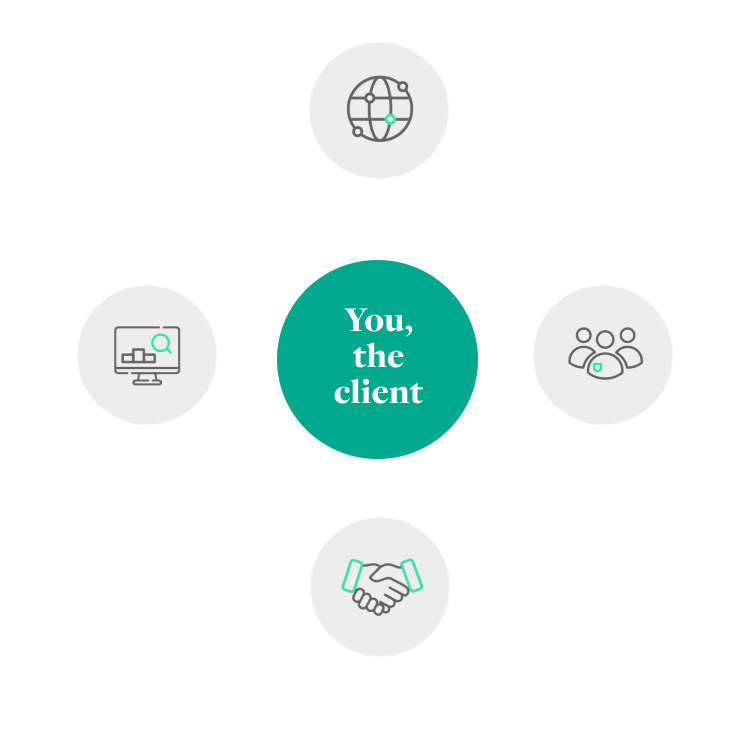
The global alternatives market went through unprecedented challenges in recent years. What you need from your service provider is a partnership approach – supporting your back and middle office operations as a reliable partner so that you can focus on value creation for your investors.
Private and Institutional Asset Owners
There has been a real and clear convergence of these two main types of asset owners globally and now they are more aligned than ever. IQ-EQ is uniquely positioned to deliver a suite of asset services tailored around the strategy and desired outcomes of all major asset owners, including both institutional and private.
Debt, Capital Markets and Corporates
Navigating debt, corporate and capital markets has never been more complex. You need a partner you can trust that understands the cultural nuances of doing business across multi-jurisdictions and whom can manage a global entity foot print with multiple reporting and governance requirements.
We are proud to help women launching their first fund
find out moreWe make life easier, more efficient and cost effective for you because we can provide everything you need in one place. You can view our most popular services below.
Support from a global, top-tier investor services group with an unrivalled service offering
Our people have the rare combination of intellectual intelligence (IQ), and emotional intelligence (EQ) that can’t be taught.
Working with IQ-EQ has been seamless – you and your team understand our business, advise us appropriately, and handle your side of our collective partnership so that we can focus on making good investment decisions. Evan Gibson SVP, Merchants Capital
We have an open and transparent relationship with IQ-EQ. I see it as more of a business partnering relationship as opposed to a transactional relationship. It is a 2 way conversation and I like that. Kunwarjit Suri EMEA Controller, F5 Inc
IQ-EQ's teams have built an approach that is both technical and pragmatic, to perfectly take into account the facts, circumstances and profiles of the portfolio companies and to produce relevant valuation methods. François-Xavier Deren Partner, LT Capital
We operate across the jurisdictions you need. Our global reach means your requirements can be taken care of 24/7
View all locationsWorking with IQ-EQ has been seamless – you and your team understand our business, advise us appropriately, and handle your side of our collective partnership so that we can focus on making good investment decisions. Evan Gibson SVP, Merchants Capital
We are always on the lookout for passionate people that possess IQ and EQ to join our growing team.
Question 1 of 3
What expertise?
Question 2 of 3
I am a:
Question 3 of 3
and I need:
Results
Recommended for you